In recent years, there has been significant improvement with how we address mobile ad fraud. If you were a User Acquisition Manager several years ago, you’d have heard only about more straightforward types of mobile ad fraud, such as bots and click spam – but now, they’re considered primitive.
Fraudsters used to refrain from using advanced technologies and sophisticated algorithms, but these have now become the norm as the app industry grows, making it more attractive for fraudsters to scam.
In the midst of all this, mobile advertisers began to examine retention cohorts, post-install events, time-to-install distribution, registration rates, and other metrics to deflect fraudsters.
In this post, we identify the key approaches used by fraudsters to fake installs via Smart Bots and Intelligent Device Farms. Let’s dive in.
Smart Bots’ mimicry and how to unveil it
Smart Bots can emulate real user behavior by faking typical in-app actions for long periods of time – some as far as 30 days. Let’s examine the most common mimicry techniques of Smart Bots:
Test groups
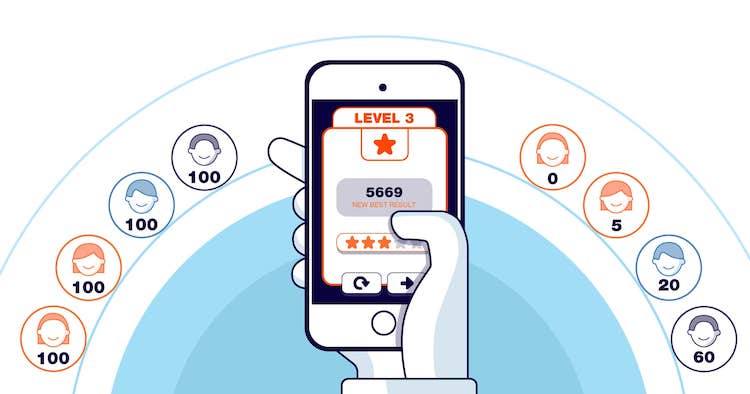
This popular technique builds multiple user groups with different behavioral models, and then injects them into the victim’s app. By testing against these groups, it’s easy to define models that count as real installs. Consider the following examples: fraudsters test four groups (A, B, C, D) with 100 users each, of which the level three reaches 60%, 20%, 5% and 0% of users, respectively.
These user groups get injected into the app by following the ad’s link and downloading the app. After receiving data on the infected paid traffic, the anti-fraud solution maps out fraudulent installs and generates an aggregated report that goes to the advertiser, who will then reject fraudulent traffic.
This fraudster modus operandi allows them to obtain reports about rejected conversions, helping them determine which groups were not discovered and which groups to rely in the future.
This approach is common for both classical and Smart Bots – but it includes a critical flaw that helps identify fraudsters: they only know the quantitative indicators of an event but remain clueless about the time distribution of these events.
CTV Growth Guide: A must-read for performance marketers
Whether you’re looking to boost brand awareness or drive user acquisition, this guide has you covered. Learn how to leverage CTV for both brand awareness and performance-driven campaigns and get actionable insights to optimize your strategies.
Download nowThus, fraudsters are unable to fully mimic the behavior of real users as they don’t have all the information about an event’s funnel and its distribution time.
SDK hacking for level-up mimicry
Fraudsters mimic user behavior by exploiting the APK file of an app with the Mobile Measurement Partner (MMP) SDK sewn into it. A hacked SDK lets fraudsters use the victim’s app to see the SDK-tracked metrics. With this tracking, it is easy to determine which values serve as the benchmark to pass as a real user. Fraudsters map the timescale of in-app events to teach Smart Bots how to fake these values to resemble a real user as much as possible.
Real user data
Apps can be openly sold and purchased along with analytics, device IDs, user IPs, geolocation, and pretty much all hardware metrics. Fraudsters obtain these records easily and see how real users interact with an app, where they tap on the screen, and when specific benchmarks are completed. That is how fraudsters bypass identifiers of MMP and train Smart Bots to mimic user behavior inside similar apps.
How to stop fraudsters from farming your budget
The share of device farms on the app install fraud market is declining. Nonetheless, it has evolved into new ways to mimic post-install activity and in-app purchases. Known as Intelligent Device Farms, these sophisticated rogue units can be pre-programmed or manually-powered:
- Pre-programmed device farms involve automatic actions in the emulating hardware. Similar to Smart Bots, fraudsters gain data about real users and mimic it on their devices.
- In manually-powered device farms, knowing what advertisers pay for (their KPIs) is enough to fake installs and claim attribution.
According to Dr. Augustine Fou, the Cybersecurity and Anti-Ad Fraud Consultant with over 23 years of digital marketing experience, fraudsters are no longer constrained by hardware capabilities. In his article, Dr. Fou points out that leveraging legitimate mobile emulators and cloud data centers, fraudsters can beat the “Judy Malware” record of over 1 billion fraudulent ad impressions per minute.
So, what can advertisers do to keep fraudsters at bay?
It is the key to identify the fraud method. For example, Intelligent Device Farms require the study of the distribution of events over time, including event funnel, time to reach an event, and time between events. Fraudsters use complex scripts to fake benchmarks based on median values, making it hard to pass up as a real user.
For instance, think about how fraudsters gain access to datasets that include information about how users complete app tutorials in 30 seconds. Thus, all fraudulent events will fall under the 25-35 second interval – as opposed to real users where the time to complete the same action fluctuates based on internet speed, reaction rates, and much more.
Ultimately, events that are “too perfect” may signal that you’re dealing with fraud. To make sure, you must examine each stand-alone install since the aggregated report alone can’t reveal the whole picture.
Don’t fall victim of intelligent fraud
Mobile ad fraud has evolved to the point where mobile advertisers can’t fight it alone. Detecting fraudulent installs requires the analysis of large volumes of parameters and correlations, which is virtually impossible without the help of an intelligent anti-fraud platform by your side.
That’s precisely where Machine learning-based solutions come in handy. Such tools help automate the analysis of data and metrics by leveraging cutting-edge technology that is based on 3 layers of machine learning algorithms, providing an outstanding 97% degree of accuracy.
Dr. Fou advises that “in addition to using app install fraud detection, use some common sense when reviewing app installs. For example, are lots and lots of installs happening at 3am in the morning when humans are asleep? Or do all of the users of the app use it at the exact same time? Fraudsters get greedy and that’s when you catch them.”